$12,500 Bug - How I Deleted Any Facebook Photo: Exploiting the Support Dashboard- Bug Bounty
Hello,
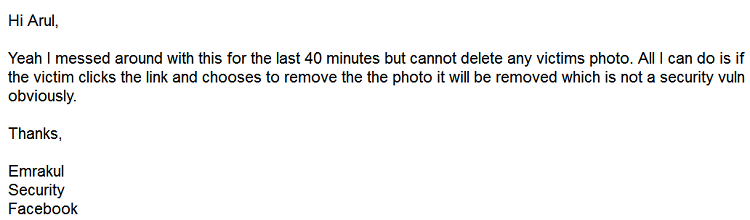
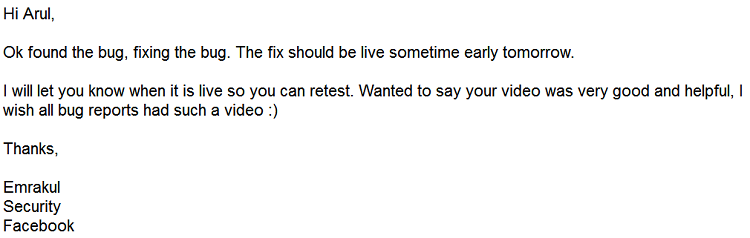
I want to share a critical bug I discovered on Facebook that allowed me to delete any photo without the user's interaction. Initially, the Facebook team was unable to reproduce the issue. However, I didn’t give up. I later provided them with a video proof of concept and a detailed explanation using demo accounts to demonstrate the bug clearly.
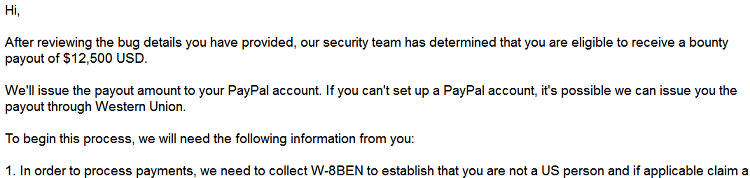
This security vulnerability has since been fully patched, and Facebook rewarded me with $12,500 for reporting it.
Initial Review
Bug Approval
Bounty Confirmation
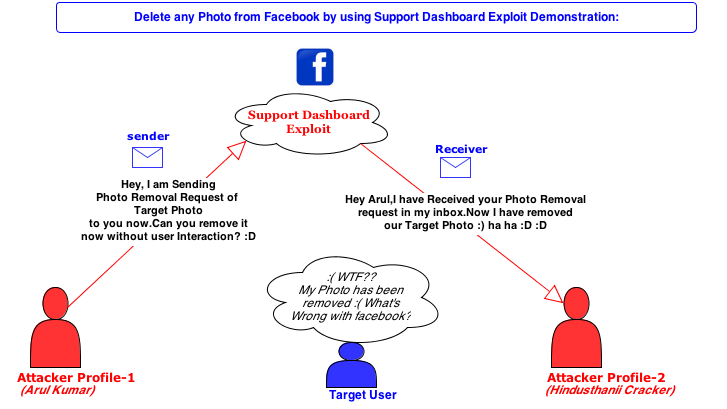
Root Cause of Vulnerability
The Facebook Support Dashboard is a portal designed to help users track the progress of their reports. According to Facebook, the Support Dashboard allows users to see whether their reports have been reviewed by their employees who assess reports 24/7.
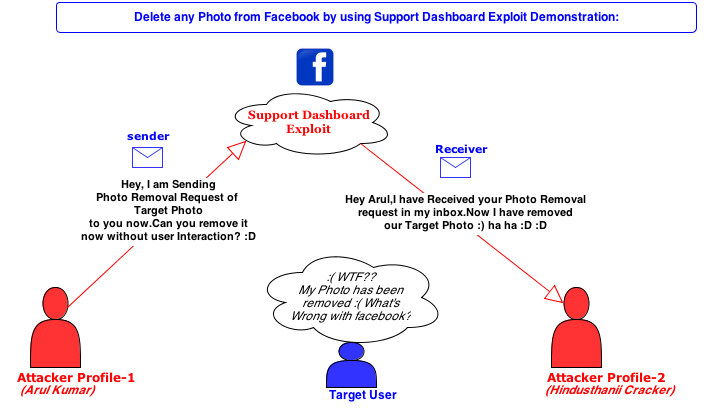
This vulnerability primarily existed in the mobile domain. In the Support Dashboard, if a reported photo was not removed by Facebook, users had the option to send a "Photo Removal Request" to the photo owner via a message. When a user sent this claim message, Facebook's server would automatically generate a photo removal link and send it to the photo owner. If the owner clicked the link, the photo would be removed.
Due to improper server-side validation, an attacker could exploit this flaw by manipulating the Photo_id and the owner's Profile_id to generate a photo removal link for any photo. The attacker would then receive the link in their messages, making it simple to remove any user's photo by accessing the link. Additionally, Facebook did not notify users when their photos were removed from their accounts.
Affected Endpoint
https://m.facebook.com/report/social/?phase=0&next_phase=8&pp={"first_dialog_phase":8,"support_dashboard_item_id":396746693760717,"next":"/settings/support/details/fbid=396746693760717","actions_to_take":"{\"send_message\":\"send_message\"}"}&content_type=2&cid=<PHOTO_ID>&rid=PROFILE_ID>In the mentioned URL, the cid and rid parameters are vulnerable, allowing an attacker to send a photo removal link for any photo to their inbox by modifying the values of "photo_id" and "profile_id".
Here:
cid= Photo_id (The target photo that needs to be removed)rid= Profile_id (The attacker's profile ID)
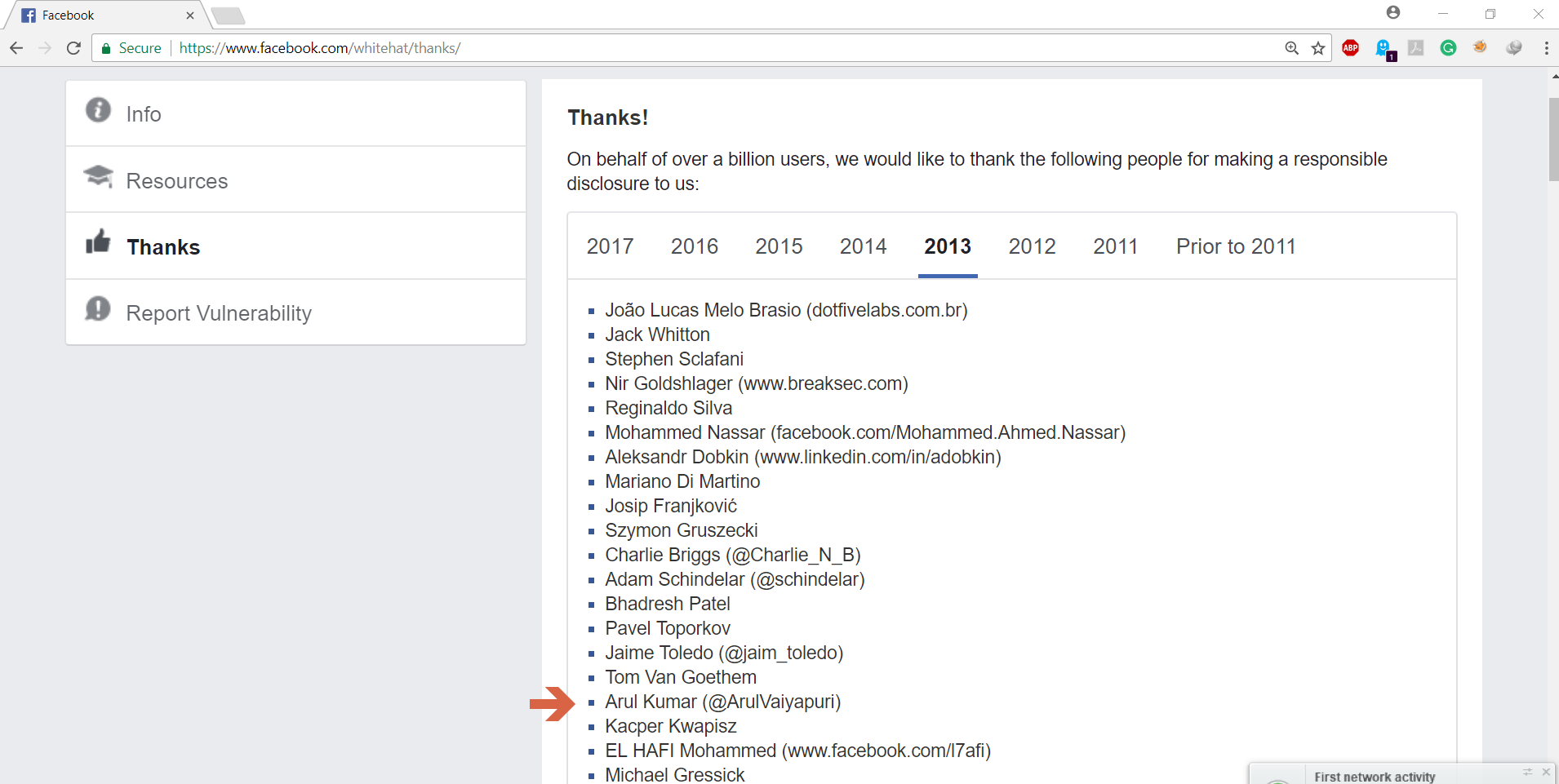
Hall of Fame
My name was added to the Facebook Hall of Fame page.
Video POC
This has been covered by several media outlets.